Reviewed By
By Brian Wallace
January 10, 2024 • Fact checked by Dumb Little Man
How To Secure Mobile Data: Tips to Protect Yourself Online

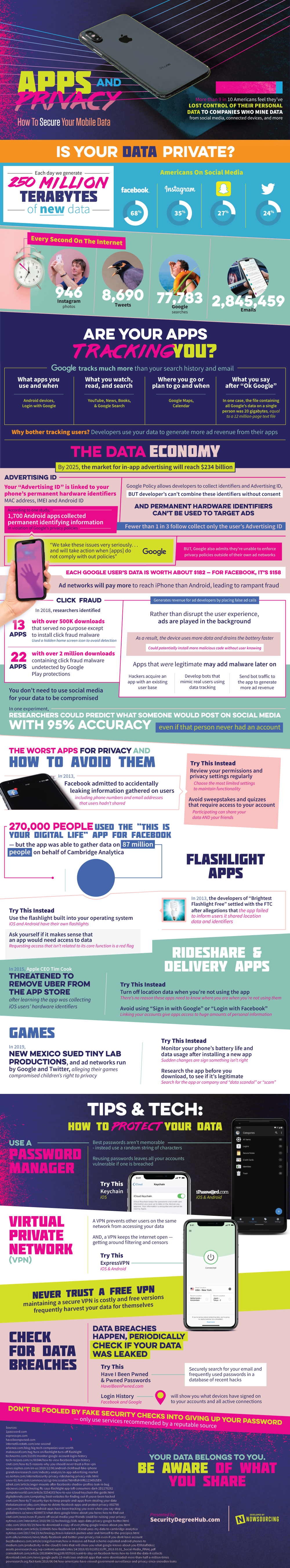
Think about all the Instagram, Facebook, and Twitter posts you make. Then, consider that for every post, there is data collected about your location, device, and more.
We create new data amounting to 250 million terabytes each day. 68% of Americans who use social media are on Facebook, 35% are on Instagram, 27% are on Snapchat, and 24% are on Twitter.
How are we to know which apps are really tracking us? And how to secure mobile data?
Google tracks a lot more than just your emails and search history. Through Android devices and Google logins, Google stores information about your app use and time of day. YouTube, (Apple) News, Books, and Google Search collect information on your search terms and reading material.
Google maps and Calendar applications know all about your travel plans and meetings, even what time of day you’re planning on going. Even more interestingly, it's possible to track every voice search as well.
The question is this:
Why bother tracking users and collecting our data in the first place?
Well, it contributes to the data economy. Developers use our data to generate more ad revenue from their available apps. For example: personalized, clickable ads appearing after you are tracking continuously when you're visiting a website, saying a brand’s name, going to a specific restaurant, or more.
In just a few years, the in-app advertising market is estimated to be valued at $234 billion.
How does it work?

Your data is accessible to developers as it is stored in your device’s memory. This file contains information about the device’s unique identifying signatures, including things like MAC address, Android ID or IMEI number.
One study found out that about 1,700 Android apps that were able to collect permanent identifying information violated Google's privacy policy.
So there are protocols in place to protect against mining data.
Here’s the complete breakdown:
Google allows the collection of certain data, but developers are restricted from combining that data without prior knowledge and consent of the user. In addition, Google restricts developers from using those unique identifiers in the process of ad targeting. As a side note, more than 2 in 3 are known to collect more than those individual unique identifiers.
On the matter, “We take these issues very seriously,” Google says. “And we will take action when [apps] do not comply with our policies.” However, enforcing privacy policies that are not within its own networks has proven difficult for Google.
So, what’s to gain?
For a Google user, their individual data cost an average of nearly $200. Facebook users’ data is worth a little less, but still highly valuable. Furthermore, advertising find iPhone users more valuable than Android users and subsequently will require a higher cost to reach the latter, which has led to documented cases of fraud.
The question is what type of fraud can be done through collecting the information stored in the Advertising ID of the average American?
Click fraud.
Researchers identified 13 apps in a 2018 study, which were available in the app store, that only existed to install click fraud malware on users’ devices. Each app had over 500,000 downloads. The icons for such apps are hidden, making them harder to detect.
These researchers also found a similar situation in the Google Play store in which 22 apps with over 2 million downloads were undetected by routine security measures and firewalls.
See Also: Can Android Become an Invulnerable System in the Future?
What’s the point?

Click fraud is able to generate revenue for different ad developers through fake ad calls. Instead of disrupting user experience, the ads are just played in the background. They are posed as a mere annoyance rather than safety issue or inconvenience.
Because of this, devices typically use more data. It also causes batteries to drain a lot faster. There's also the risk of getting more malicious codes installed without the user knowing or being alerted.
Saying this, do not be confused. Even if you have never used social media, your data can still be compromised.
There are several applications guilty of tracking your data outside of those social media developers have released. Continue reading to find out how to secure mobile data through apps and protect your privacy.
Source: Security Degree Hub
What Do You Think ?

















Frequently Asked Questions (FAQs)
More Like This
More from Dumb Little Man
Brian Wallace
Brian Wallace is the Founder and President of NowSourcing, an industry leading infographic design agency based in Louisville, KY and Cincinnati, OH which works with companies that range from startups to Fortune 500s. Brian also runs #LinkedInLocal events nationwide, and hosts the Next Action Podcast. Brian has been named a Google Small Business Advisor for 2016-present and joined the SXSW Advisory Board in 2019.
Because being “in the know” is kinda hot.
Smart, funny, sometimes spicy content we handpicked so you don’t have to.