Reviewed By
By Amelia Matthers
July 25, 2019 • Fact checked by Dumb Little Man
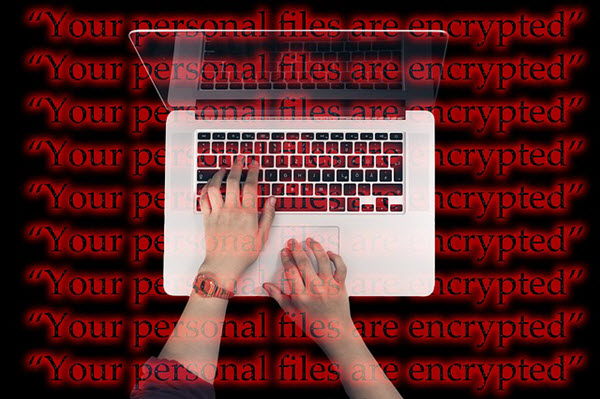
The Most Devastating Cyber Attack: How to Prevent Ransomware

Large corporations, governments, and even small businesses are always at a high risk of being attacked. Hackers and cybercriminals aim to steal your money no matter who or what you are. Cyber-attacks have an increase of 235%, according to a report issued by Malware Labs in 2019.
Malware, Man-In-The-Middle, and phishing are some of the most common types of cyber attacks, but which could be more destructive? The answer is ransomware.
Ransomware is on the rise in the cyber world. It is a type of malware attack that will steal your data. Criminals will demand ransom to return your data.
In the U.S., Cleveland Hopkins International Airport and Baltimore City faced ransomware attacks. These drove smaller businesses, thinking that large corporations and governments are the only targets of a ransomware attack.
The truth, however, is that every business should prepare itself to prevent this attack. Every business needs to know how to prevent ransomware.
Difference between ransomware and other cyber attacks

Ransomware doesn’t lack confidential information or personal data to be effective. This distinct behavior makes it different from other cyber attacks. It surfs for data in an organization that is valuable enough for the victim to pay the ransom just to get them back.
Ransomware is a very effective approach of hackers to paralyze an organization. It restricts their access to their information, deliver services, and accept payments. All these obstacles will turn customers of an organization away.
How to Prevent Ransomware
Ransomware can cost a lot to a business so it must prepare itself to combat not only ransomware but all kinds of cyber attacks.
Several best practices businesses should implement to protect themselves from cyber attacks include:
Security Software
Security software is crucial for an organization to detect and deter fraudulent activity. This software should be strong enough to verify activities and detect potential harm to the organization.
If your business is online, then your organization must use an identity verification service. It is an anti-fraud technology for online businesses that can verify your customer and even employees online. It is capable of detecting if someone is pretending to be someone.
Firewall & Intrusion Detection/Protection
Installing a firewall is a crucial security measure and any business should not neglect it. It can deny and allow access to a company network or a part of the network. By restricting access with the help of a firewall, an organization can prevent scammers.
Web & Email Filtering
All efforts of preventing ransomware from getting in the network become useless when an end-user inadvertently opens a malicious email and click a malicious link. For end-users, it is becoming increasingly complex to detect all malicious emails as phishing attempts are becoming more sophisticated.
By email safety awareness training and email filtering for employees, an organization can mitigate the risk. It's one of the best ways on how to prevent ransomware.
User Education
Users/clients are the most valuable asset of a company. Their protection should be the priority of any organization. An organization should arrange regular awareness programs for users to educate them about malicious links and persons.
See Also: 5 Top Cyber Security Training Tips For Employees
Backup offers the best protection
Taking backup on regular basis can secure you from ransomware. In case you become a victim of ransomware, you can use your previous backup to keep going. Usually, taking backup costs you little to nothing but restoring backup could take days or weeks. It will cost you in labor and downtime to restore and recover your systems to make them fully functional.
Various types of backup, disaster, and threat prevention strategies are circulating in the market and every solution is valuable according to its use. You can protect your business by implementing a solution that mitigates risks attached to your business.
Your IT team or technical department should understand and analyze business deeply to provide and implement the best solution for unique problems. An IT team must identify which type of backups are beneficial for specific organizations and how to restore them more efficiently in less time in case of any critical situation.
What Do You Think ?

















Frequently Asked Questions (FAQs)
More Like This
More from Dumb Little Man
Amelia Matthers
I’m currently writing articles for multiple blogs and I’ve experience of almost 4 years in creative and technical content writing. I’m writing articles on professional platforms and reputed companies such as medium and blogger. I’ve great knowledge about artificial intelligence, machine learning, big data & Verification Services. This is the reason I can write quality content for any technical field.
Because being “in the know” is kinda hot.
Smart, funny, sometimes spicy content we handpicked so you don’t have to.